OIDC Implementation
Clever Complete Agreement RequiredThis feature is included with a Clever Complete subscription. Sign up here or email your Application Success Manager to learn more.
Use this page to implement OpenID Connect (OIDC) with Clever, configure third-party identity services, and understand how identity tokens and the /userinfo endpoint work.
Overview
OpenID Connect (OIDC) is the protocol Clever uses for user authentication. While OAuth 2.0 focuses on authorization, OIDC focuses on identifying who the user is.
If you are building an OIDC integration with Clever, the flow is almost the same as the OAuth flow. The key differences are:
- your application can receive an identity token
- you can use the
/userinfoendpoint as part of the OIDC flow
Get set up for OIDCTo use OpenID Connect with Clever and receive identity tokens, contact Clever Support to have your application configured for OIDC.
OAuth and OIDC data access
Access tokens
Access tokens acquired through the Clever OAuth flow do not grant full Data API access. They can only access:
/me— returns the tokentype, Clever user ID, and district ID/districts/{id}— whereidis the district Clever ID/users/{id}— whereidis the user Clever ID
If you need full roster access, use Secure Sync.
Identity token claims
If your application is configured for OIDC, Clever can return an identity token with these claims:
user_id— the Clever user ID for API versions before v3.0user_type—student,teacher,staff, ordistrict admindistrict— the user’s Clever district IDmulti_role_user_id— the Clever user ID for API v3.0 and lateremail— the user’s email, if availableemail_verified—falseby default; contact Clever Support if you need this claim to betruegiven_name— the user’s first namefamily_name— the user’s last name
Identity token metadata
Identity tokens also include standard metadata claims:
iss— alwayshttps://clever.comsub— the multi-role Clever user ID used for API v3.0 and lateraud— your application client IDiat— the token creation timeexp— one hour after token creationnonce— used to prevent CSRF; this must match thenoncevalue from the original/authorizerequest when provided
Multi-role users
user_idandmulti_role_user_idare different values.multi_role_user_idmatchessub.
Working with third-party authentication services
One advantage of OIDC is that many third-party authentication services can connect to Clever with only a small set of standard configuration values.
The discovery endpoint
OIDC providers publish configuration details through a discovery endpoint. Clever’s discovery endpoint is:
https://clever.com/.well-known/openid-configuration
In many cases, all you need to know is:
- Clever supports OIDC
- the issuer is
https://clever.com
The discovery endpoint tells your authentication service where to:
- start authentication
- exchange tokens
- validate tokens
Example configuration
Most third-party authentication services only require a few values to connect to Clever. The example below uses AWS Cognito, but the same general fields appear in many services.
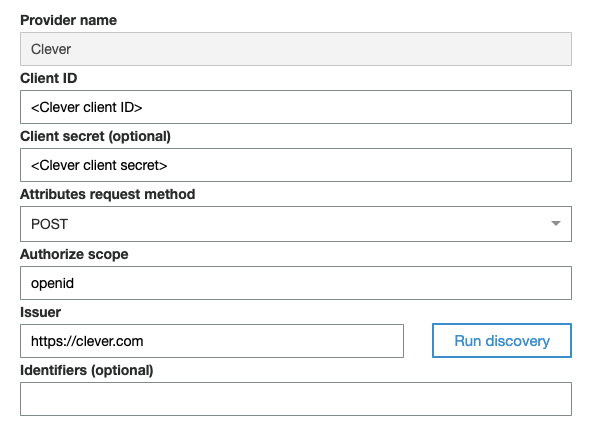
Example OIDC configuration for AWS Cognito
Typical fields include:
- Provider name — any label you want to use, such as
Clever - Client ID — your application’s client ID from the Clever dashboard
- Client secret — your application’s client secret
- Attributes request method — Clever supports both
GETandPOST - Authorize scope — Clever manages scopes through application configuration, but some providers still require
openid - Issuer —
https://clever.com
OIDC flow
The OIDC flow is similar to the standard OAuth flow, but it is designed for authentication and identity verification.
Clever’s OIDC discovery endpoint is:
https://clever.com/.well-known/openid-configuration
The flow looks like this:
- A user initiates login.
- Clever authenticates the user if needed.
- Clever redirects the user to your application’s redirect URI with an authorization code.
- Your application sends that code to Clever’s token endpoint.
- Clever returns an identity token and access token when your app is configured for OIDC.
- Your application verifies the identity token and, when needed, uses the access token with
/userinfoor other allowed endpoints.
For the full login initiation patterns, see OAuth Implementation.
Limitations
OIDC limitationsIdentity tokens are not available for Clever Library integrations.
If you are building for Clever Library, use the
/userinfoendpoint instead:https://api.clever.com/userinfo
The access token can also be used with the /userinfo endpoint as part of the OIDC flow.
Updated about 2 months ago
